Spring4Shell zero-day RCE vulnerability
Apr 01, 2022 | Security Advisory
The world got another shock yesterday when news of the disclosure of a PoC for an unauthenticated Remote Code Execution zero-day vulnerability in Spring Core, a famous framework for building Java-based enterprise applications.

Summary
org.springframework:spring-beans is a package that is the foundation for Spring Framework's IoC container. The BeanFactory interface supplies a configuration mechanism that operates any type of object.
Affected versions of this package are vulnerable to Remote Code Execution via manipulation of ClassLoader which is likely with a POST HTTP request. This could allow an attacker to execute a webshell on a victim's application.
Note: This is only exploitable when an application is built with both JRE version of 9 or above and Tomcat WAR deployment version 9 or above.
These are the prerequisites for the exploit:
JDK 9 or higher
Apache Tomcat as the Servlet container
Packaged as WAR
spring-webmvc or spring-webflux dependency
PoC
1/ docker run -d -p 8080:8080 gcr.io/snyk-security/exploits/spring4shell:pre-invoke-with-python
2/ [get the running container name w/ docker ps] docker exec -it <PS> /bin/bash
3/ cd /opt
4/ python3 exp.py --url http://localhost:8080/handling-form-submission-complete/greeting
5/ [assuming you still using localhost and not changing hosts] in your browser, go to: http://localhost:8080/handling-form-submission-complete/tomcatwar.jsp?pwd=j&cmd=CMD
and change CMD to any Linux cmd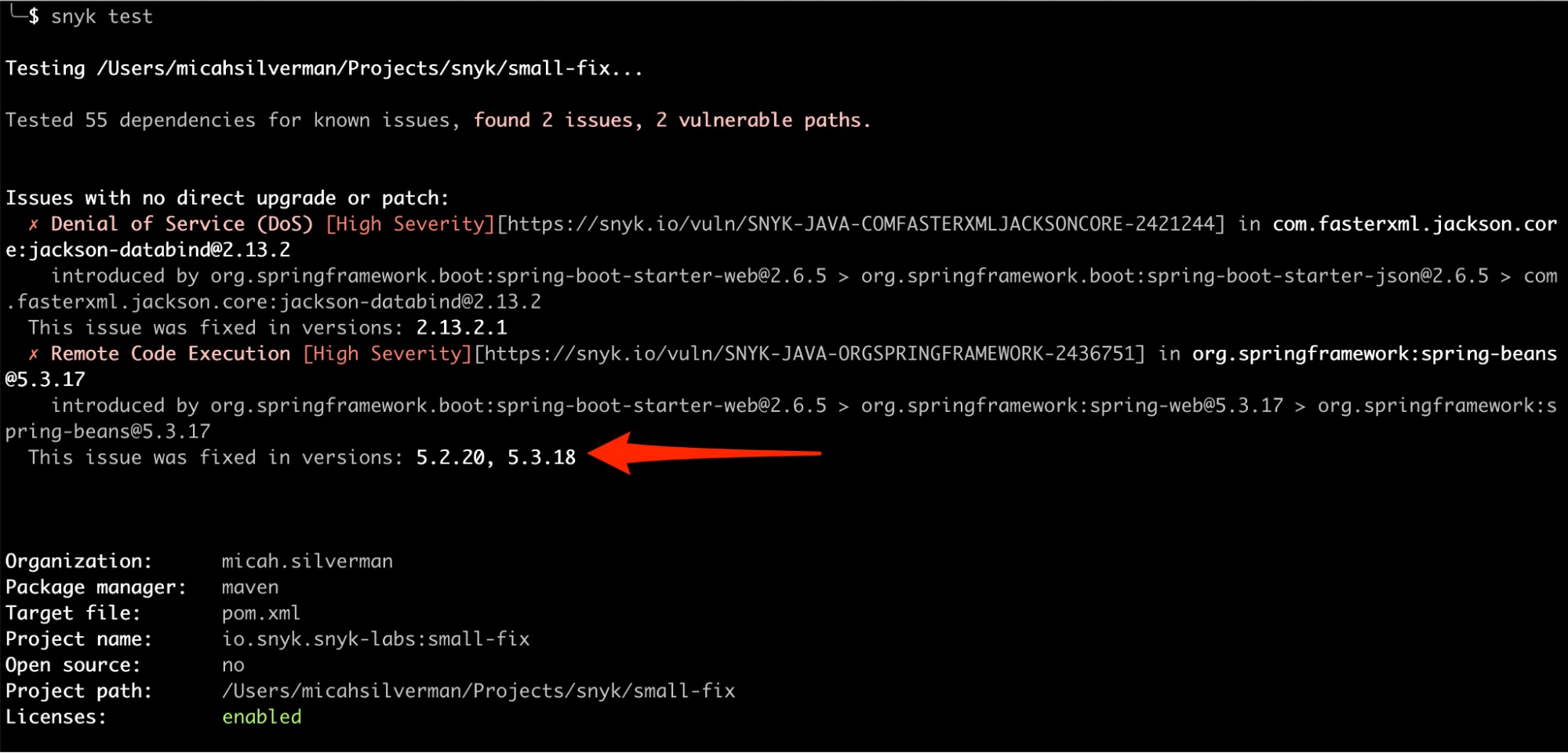
Snyk’s tools have already been updated to notify you if your application is vulnerable
“Actions to Take Today to Protect Against Spring4Shell vulnerability in Spring versions 5.3.18 and 5.2.20 and an official CVE has been published as CVE-2022-22965”
Mitigation
Affected versions should apply the following mitigation: 5.3.x users should upgrade to 5.3.18+, 5.2.x users should upgrade to 5.2.20+. No other steps are necessary. Releases that have fixed this issue include:
Spring Framework
5.3.18+
5.2.20+
Spring Boot, use version
2.15.12or2.6.6
How do I know if I’m vulnerable?
There are a few requirements for an application to be vulnerable:
You use a Spring app (up to and including version 5.3.17)
Your app runs on Java 9+
You use form binding with name=value pairs – not using Spring’s more popular message conversion of JSON/XML
You don’t use an allowlist –OR– you don’t have a denylist that blocks fields like “class”, “module”, “classLoader”
So, what is Spring4Shell?
As of Wednesday, March 30, the Contrast Security Labs confirmed the 0-day vulnerability by use of a public POC, Spring4Shell, which could be the source of Remote Code Execution (RCE)
Yesterday, an exploit for a zero-day RCE in the Spring Framework dubbed 'Spring4Shell' was briefly published on GitHub and then removed.
Exploitation requires an endpoint with DataBinder enabled (e.g. a POST request that decodes data from the request body automatically) and relies on the servlet container for the application, permitting an adversary to call getters and setters to write a malicious JSP file to disk.
References
https://snyk.io/blog/is-there-such-a-thing-as-spring4shell/
Disclaimer
The information provided in the Arcane Security Advisory is provided "as is" without warranty of any kind. Arcane disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Arcane or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits, or special damages, even if Arcane or its suppliers have been advised of the possibility of such damages.
Tags: #cve-2022-22965 #rce #spring4shell #security-advisoryHave questions? Let's talk