Vulnerability Risk Management
Gain clarity into risk and focus on exploitable vulnerabilities first
Vulnerability vs. Exploitability, why does it matter?
A vulnerability is an unlocked door, an exploit walks through the door. This analogy is important when it comes to exploitable vulnerability. While the idea of having a critical vulnerability in company assets seems risky, having an easily exploitable vulnerability is riskier.
Well, What's the difference? How do you prioritize thousands of vulnerabilities in real-time?
Vulnerabilities are by definition a weakness in a defined environment, so being vulnerable is having a weakness in your assets, which means that an adversary could potentially take advantage of an asset(s) to gain elevated privileges or access to other resources. On the other hand, exploitable vulnerabilities indicate that vulnerability has been enriched with offensive methods and a definite attack path to providing malicious access to target resources.
Vulnerability exploitations in the wild used to be the best indicator for which vulnerabilities should prioritize and increased risk posture.
Insight VM Vulnerability Management Platform
Vulnerability management is the life cycle process of identifying, assessing, mitigating, and reporting security vulnerabilities in systems and software before they are exploited. The Vulnerability Risk Management (VRM)process is vital for every organization to prioritize imminent threats and minimize their "attack surface."
Based on how fast vulnerabilities can be exploited, organizations must be prepared to perform remediation processes on assets.
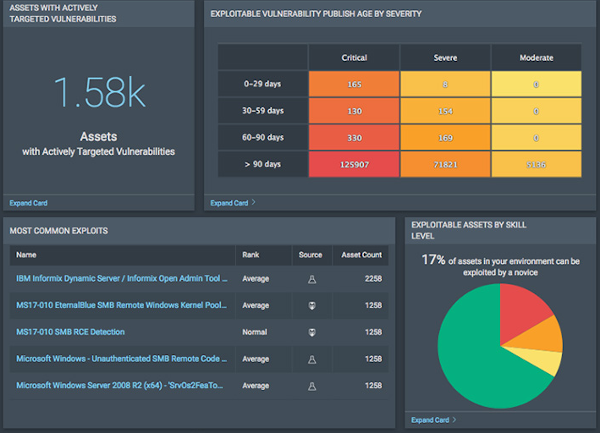
The Rapid7 Insight platform, together with Rapid7's vulnerability research, exploit knowledge, global attacker behavior, exposure analytics data, and real-time reporting to provide an actionable, scalable, and efficient way to analyze vulnerability data, real-risk prioritization, and help remediation processes.
InsightVM leverages Insight Platform for live vulnerability and endpoint analytics so decisions can be made about how to best remediation. Get an effective and proactive approach partnered with Rapid7 by Arcane.
Have questions? Let's talk
Arcane experts are ready to answer your questions