New DNS vulnerability put IoT devices at Risk
May 05, 2022 | Security Advisory
A vulnerability in the DNS standard library written in C programming language that is widely used in IoT products may put devices at DNS poisoning attack.
A threat actor can use DNS poisoning to redirect the victim to a malicious website owned by the attacker instead of the legitimate location. The Standard C library of uClibc and uClibc-ng are widely used by embedded devices (specifically designed for OpenWRT) like Netgear and Linksys, and many Linux distributions.
The flaw is caused by the predictability of transaction IDs generated by the library, which may allow attackers to perform DNS poisoning attacks against the target device said Nozomi Networks Researchers Giannis Tsaraias and Andrea Palanca
Vulnerability Details
The flaw is caused by the predictability of transaction IDs automatically generated by the library, the adversary can perform DNS poisoning attacks on vulnerable devices, and they can also perform MiTM attacks. That offensive method allows attackers could steal or manipulate transmitted information and perform other attacks against vulnerable devices. Currently, no fix is available for the vulnerability, which may be tracked with ICS-VU-638779 and VU#473698 (no CVE yet)
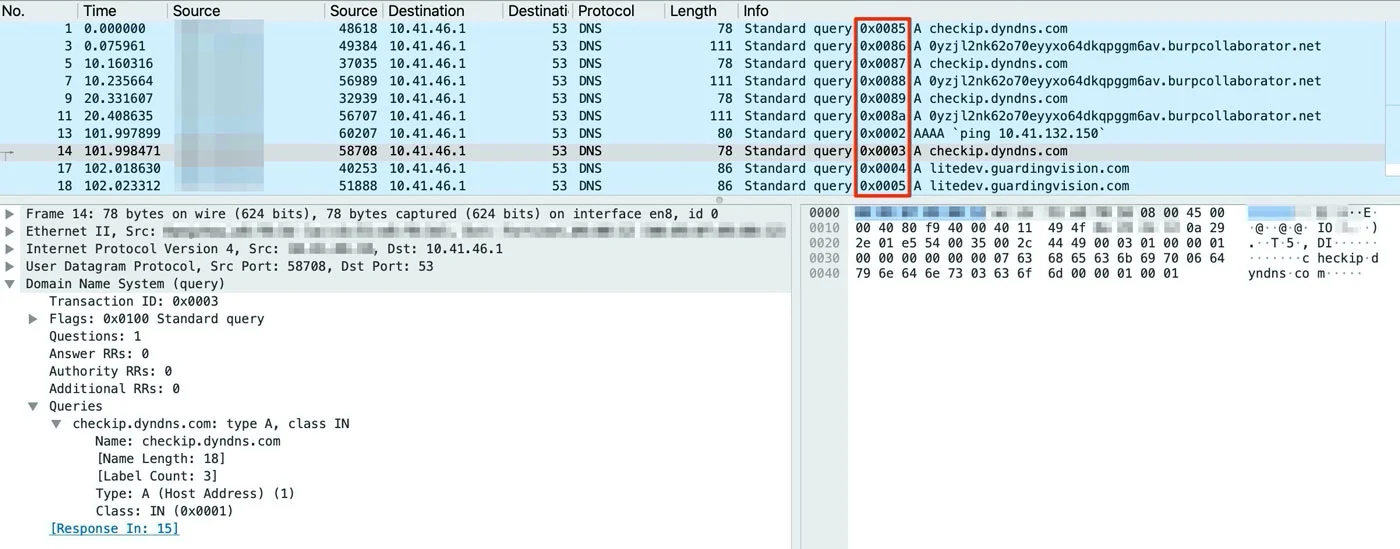
The impact of an exploit could be significant, DNS poisoning attack, an attacker is able to deceive a DNS client into accepting a forged response, thus attacker may intercept network communications and reroute network traffic to a malicious server. Exploitability relies on the ability of the attacker to brute-force the 16-bit source port value by sending multiple DNS responses.
Disclaimer
The information provided in the Arcane Security Advisory is provided "as is" without warranty of any kind. Arcane disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Arcane or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits, or special damages, even if Arcane or its suppliers have been advised of the possibility of such damages.
Tags: #security-advisory #dnsHave questions? Let's talk